The costs of a data security breach can cause a small business to go out of business, and hackers do not seem to be slowing down. People, specifically your employees, can unintentionally be the weakest link in your security system by reusing passwords across systems, selecting weak passwords, or falling prey to phishing scams. Multi-factor authentication adds a failsafe when your employees’ credentials are compromised and each layer makes it more difficult for hackers to access your data and software systems.
What is Multi-Factor Authentication?
In computer terms, authentication is the process by which a computer system verifies the user is authorized to access the system. The most common form of authentication is a username and password combination. Password requirements have become more demanding over the years, requiring longer passwords with a combination of capitalized letters, lowercase letters, numbers and special characters. Despite these requirements, passwords are only one layer of security and can be hacked via guessing, brute force methods, and stealing employee’s devices with saved passwords.
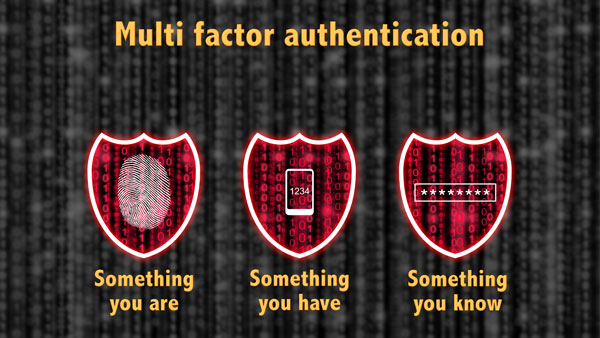
Multi-Factor Authentication (sometimes referred to as MFA) uses two or more security layers to authenticate a user. These layers can be categorized as “something you know, “something you have,” and “something you are.” Username and password combinations are used in multi-factor authentication and count as “something you know.” A second authentication layer such as an SMS text message sent to your smartphone would fall into the “something you have” category. Finally, biometric scans of fingerprints or irises are used less often but would qualify for the “something you are” category.
Social media accounts, cloud applications including SalesForce.com, DropBox and Office 365 are some of the most likely applications to use multi-factor authentication. Your business may already be using these applications or similar tools for marketing, selling, sharing files, and collaboration between employees and customers. Businesses also use MFA for VPN connections, which allow your employees to securely connect to your business’s IT systems from remote locations. As you can imagine, MFA plays an important role in ensuring the users that log in to these business systems are who they say they are.
What Should Small Businesses Consider When Selecting Multi-Factor Authentication Solutions?
- Cost. Look for Multi-Factor Authentication solutions that are cost-effective and make smart choices when deciding what and how much to protect. Does every software system need MFA, or only a few business-critical systems? Does every employee need a specialized hardware token, or will using their existing smartphones meet your needs? Are there existing MFA plugins to cloud-based software that you can leverage for your authentication needs?
- Ease of Use. Keep the user experience in mind when selecting an MFA solution. If your employees find it too difficult to use, their productivity may decrease or they will look for ways to circumvent the security system.
- Backup Plan. What plans do you have in place if the employee forgets their smartphone and needs to log in? Are there additional methods to verify their identity?
arielMIS Can Help
arielMIS recommends our clients implement multi-factor authentication on all cloud-based applications, social media accounts, and remote access.
Here are some of the solutions we help clients implement:
- Google Authenticator. This uses an app on your phone to generate a one-time password and acts as a software-based token. After entering your username and password, a one-time password from Google Authenticator is used to verify the user’s identity.
- LastPass Authenticator. This is also a smartphone app that generates one-time codes for logging into applications. It can be configured to notify users of logins, generate codes, and for some systems enable one-click secure logins.
- RSA SecureID. An enterprise-level authentication solution that provides a variety of methods for authentication including push notifications, text messages, biometrics, hardware and software tokens, and more.
- VPN Connection + Secure Remote Desktop This double layer of security requires remote users to have the correct VPN credentials and connection before connecting to a secured remote desktop that requires its own credentials. This process limits the devices and computers that can access secure data, making it difficult for hackers to collect all the pieces needed to gain control of your systems.
arielMIS is a Managed Service Provider (MSP) providing businessCARE™ IT services designed to keep you and your employees productive and safe. Contact Us if you're interested in learning more about our services.